Rules are made to be broken but are also made for a reason. Our ‘go to’ is the widely known ‘rule of thirds’ and is considered in the majority of our intentional compositions. But what other compositions do we use?
1 - Golden Spiral :
Based on the Fibonacci numbers, this composition uses arcs infinitely resembling a spiral shape, which can be used to create balanced and aesthetically pleasing photos.
2 - Cross :
A simple but harmonious composition using two lines, creating a midsection crosshair with the subject in the center of the frame.
3 - Tunnel :
Similar to ‘leading lines’ tunnel composition is used to draw your eye to a subject using depth.
4 - L Shape :
The L-shape composition appears when the elements create the “L” shape which can be (and often is) multiplied. The static horizontal and vertical lines this kind of composition presents create the feeling of rest, stillness, and harmony.
5 - S Curve :
The curved lines in an S-curve composition add a sense of movement to an otherwise static image. Sometimes, they can even add visual depth and perspective to the shot.
6 - V Shape :
Not only can a V lead the eye quickly to the focal point, but it can also lock the viewer’s focus on the subject.
7 - Circular :
A circle offers a different path to composition, a path where curves in the scene work well, but straight lines can tend to be at odds with the border. The circle represents a framing element that is far closer to how we actually see the world.
8 - Pyramid :
With the stable triangle composition, there is a symmetric arrangement of elements. Our example shown above is quite ‘literal’ but this composition can work using multiple elements within a frame making a ‘pyramid’ shape to keep the attention at the image axis.
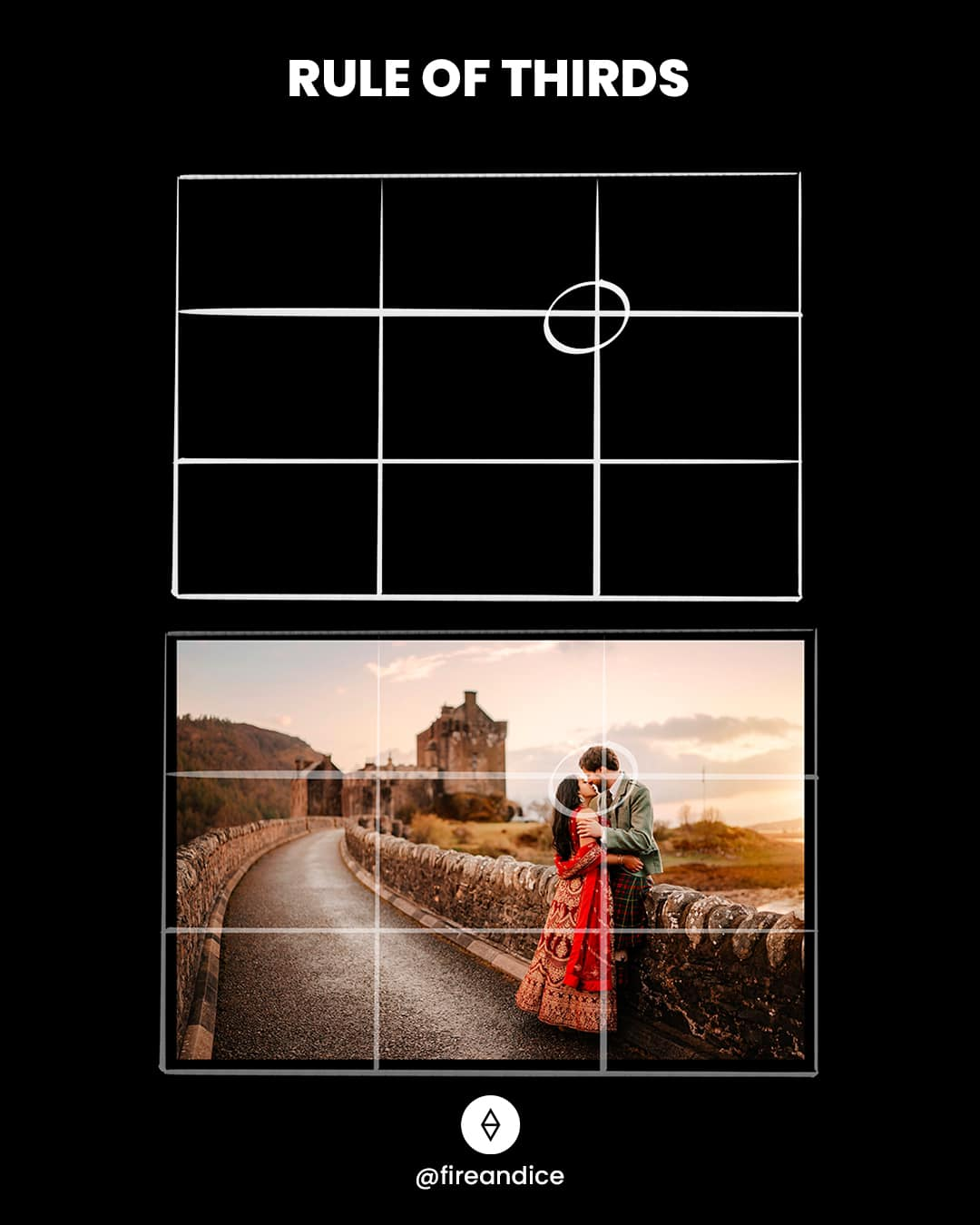
9 - Rule of Thirds :
A grid is used to divide a photo into nine equal parts, offering four crosshairs for placing important subjects. This guide helps balance your main subject with negative space.
10 - Balanced :
If you think of each element in your frame as having actual weight, a balanced composition offers two focus points of the same ‘weight’ i.e. size, sharpness, and color. An evenly balanced composition creates a feeling of calmness and peacefulness.
11 - Unbalanced :
This composition often relies on depth and asymmetry and can create emphasis in a photo by prioritizing one focus point over another.
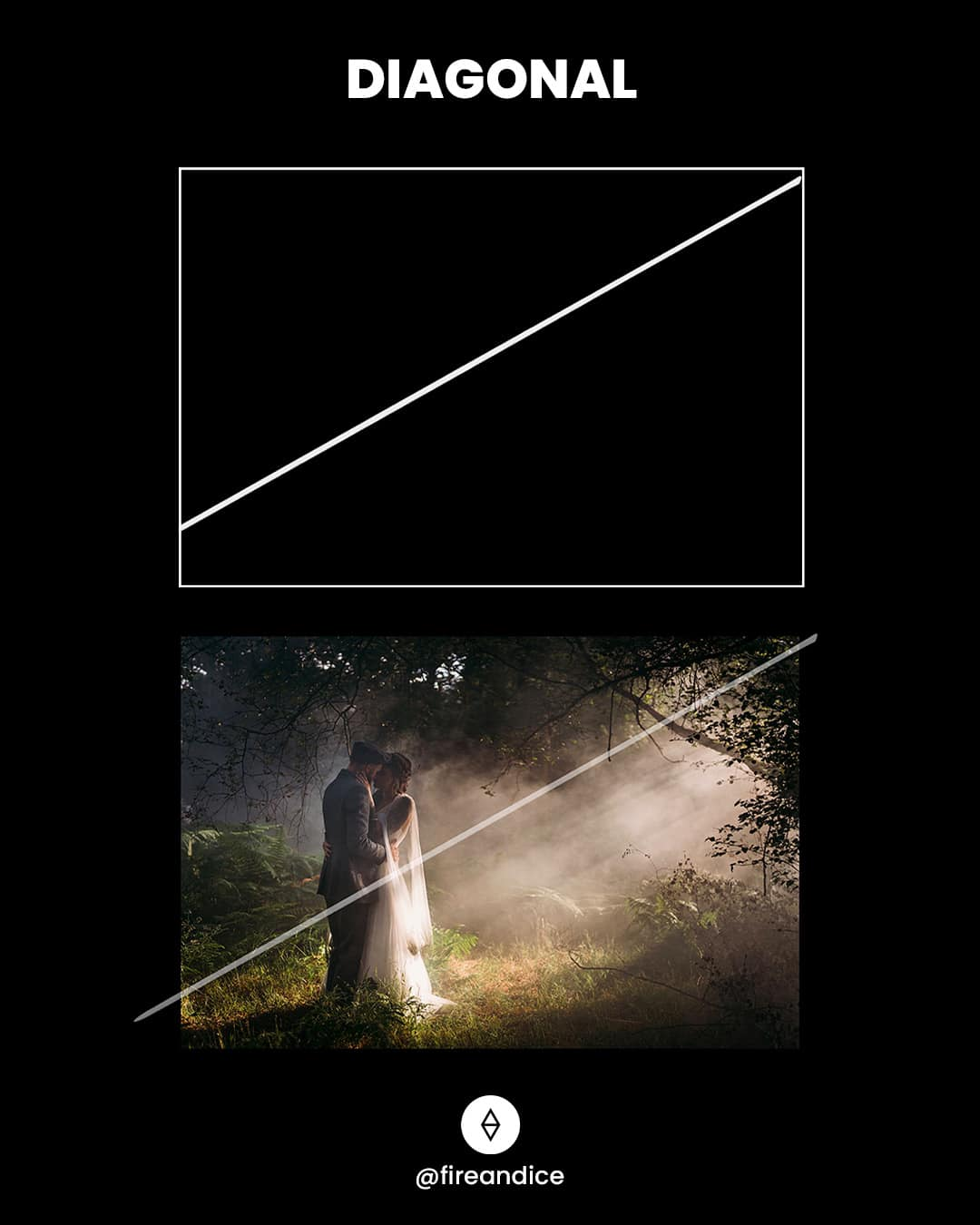
12 - Diagonal :
We often use diagonal lines to lead the eyes of the viewer through the scene, towards the subject. Therefore diagonal lines can create a sense of dynamism and action.
13 - Double Diagonal :
You can use more than one diagonal line in your frame, especially when they work together to create harmonious leading lines to highlight your subject.
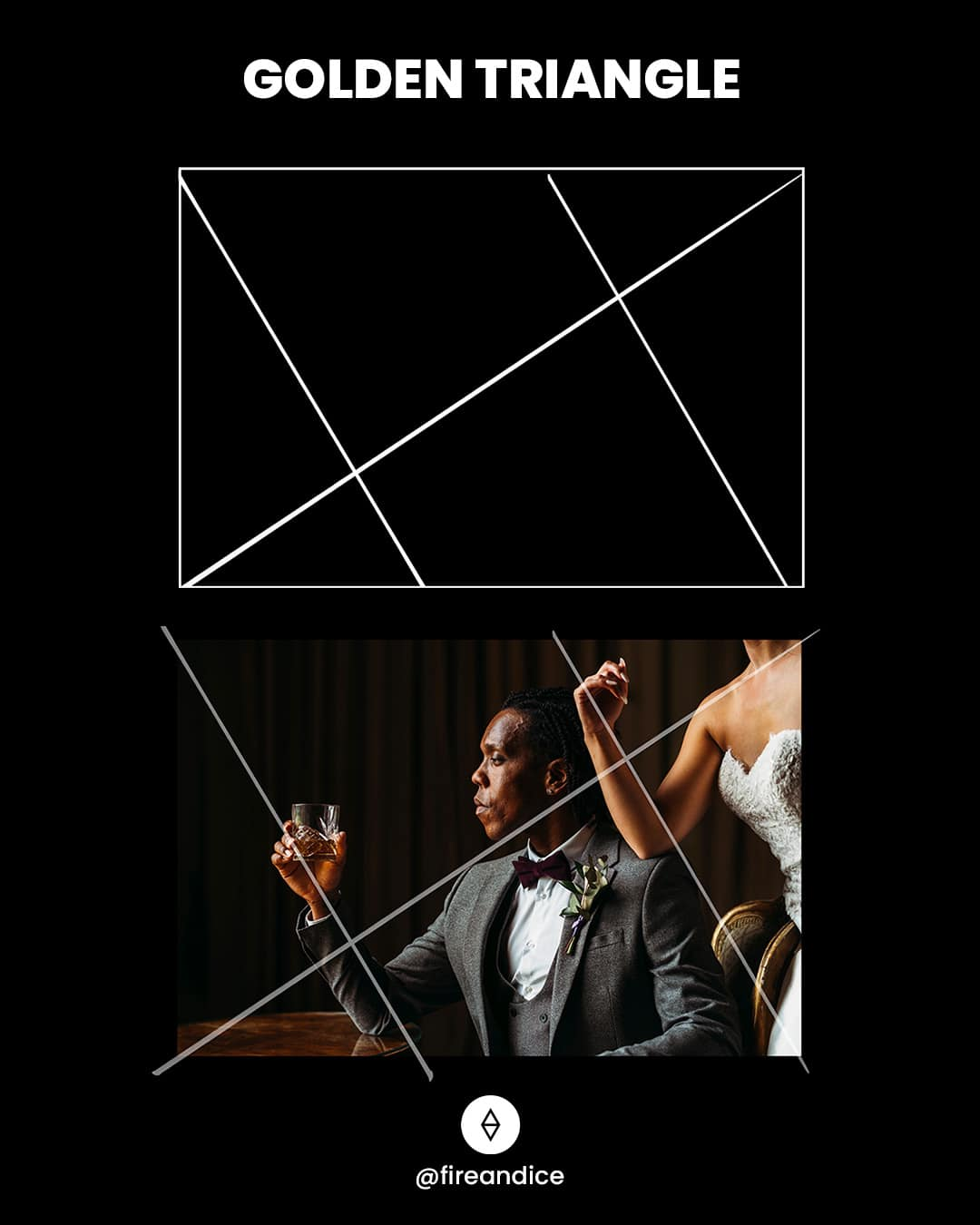
14 - Golden Triangle :
This rule is somewhat like the rule of thirds, but instead of straight lines, a series of diagonal lines form right-angle triangles. The main subject(s) should sit at the intersection of these triangles.
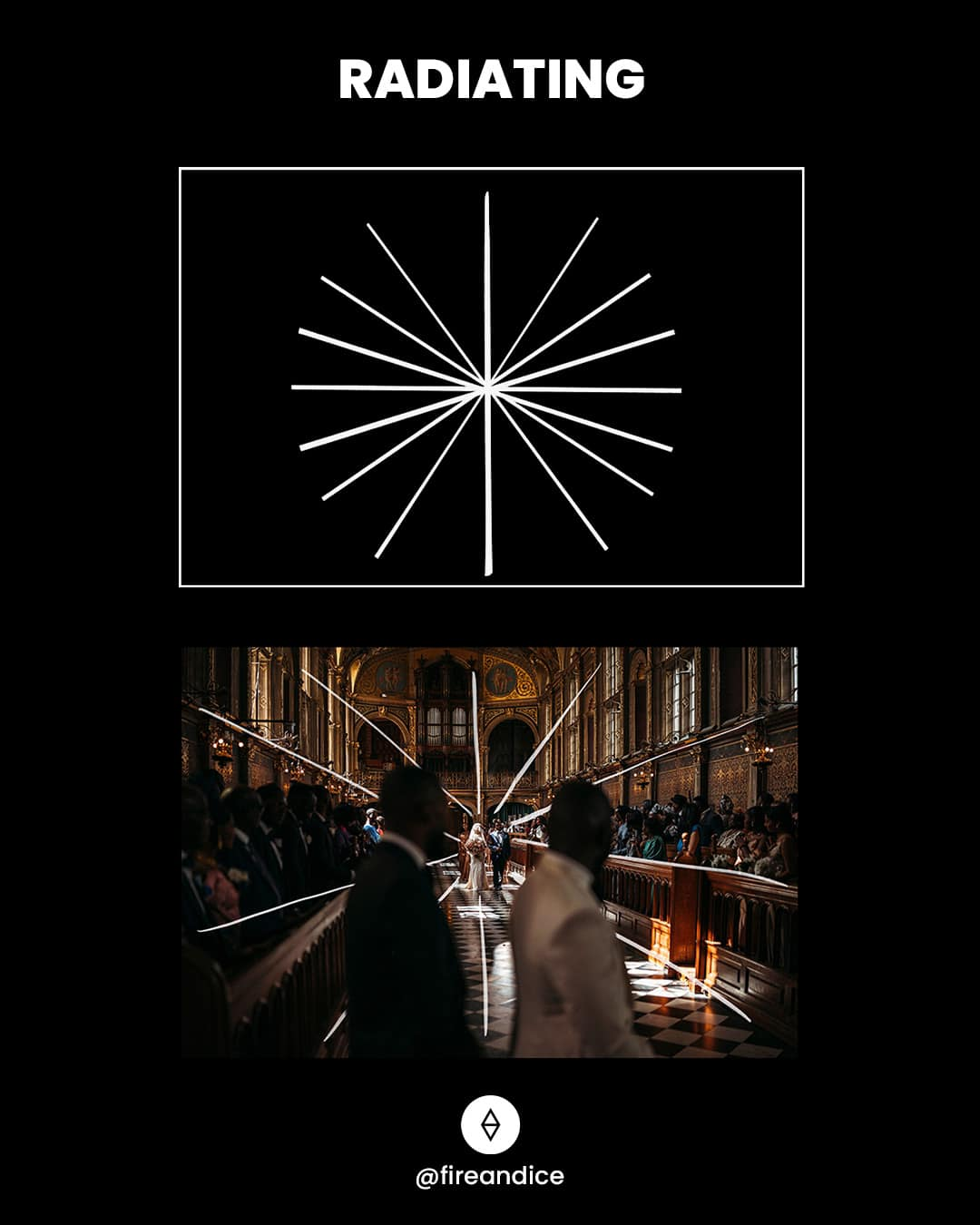
15 - Radiating :
Elements within your composition radiate outwards or inwards from a central point, adding depth and visual movement to the photo. This composition can create a sense of unity and fluid motion.
A good photographic composition is the foundation of an image and relies on the placement of the subject within its frame. Implementing these rules, and intentionally considering them can seriously up your photography!
Post Collected From Facebook - #fireandice
#weddingphotography #weddingphotographer #weddingphoto #photocomposition #goldenratio #goldenspiral #ruleofthirds #photography #photographytips #SharmaGuides











Comments
Post a Comment
Please do not enter any spam link in the comment box.